5 types of cyberattacks target everything from food to pipelines to democracy

- Cyber conflict involves a range of strategies, from traditional espionage to cyber sabotage to election interference.
- A major growth sector in cyber warfare involves ransomware attacks for profit.
- Cyberattacks are growing in number and sophistication.
Cyber conflict has a variety of forms. The first is regular state-based espionage for information. For example, as documented in a Center for Strategic and International Studies (CSIS) report, in 2013 Chinese hackers stole US weapon designs and targeted civilian and military maritime operations in the South China Sea. In the same year, as Edward Snowden revealed, the United States conducted cyber espionage against Chinese targets. The 2020 SolarWinds attack by a branch of Russian military intelligence penetrated the US Departments of the Treasury and Homeland Security and multiple private entities.
A second is espionage for industrial technology, done by both private and public actors and combinations of the two. As one of many examples, as early as 2011, the FBI reported $11 million in losses of US businesses to Chinese trade companies. In 2021, Russian and Chinese intelligence services targeted the European Medicines Agency and stole documents related to COVID-19 vaccines and medicines. In 2022, the cybersecurity firm Cyberreason reported a “massive Chinese hacking of trade secrets” by Winnti APT Group, “which specializes in cyber espionage and intellectual property theft and is believed to work for Chinese state interests.”
A third is ransomware attacks for profit, a major growth sector for the cyberworld. In 2021 alone, Colonial Pipeline was the target of a ransomware attack by DarkSide, a Russian hacking group, and JBS, the world’s largest meat-processing company, was the victim of a ransomware attack by the Russian group REvil.
The Colonial Pipeline is the largest pipeline of refined oil products in the United States—stretching from Texas to New York and carrying 3 million barrels of fuel each day. The DarkSide attack consisted of a very ordinary password breach of security—even though Colonial Pipeline had invested $200 million into IT systems, which included cybersecurity—and resulted in an extreme gas shortage in the southeastern United States. The CEO of Colonial Pipeline made the decision to pay the $5 million/75 bitcoin ransom and then notify the authorities. The US Department of Justice was later able to recover at least $2.3 million (60 bitcoin) in cryptocurrency.
REvil’s attack on JBS resulted in a cyberbreach that shut down operations in the United States, Canada, and Australia. JBS quickly paid the $11 million ransom in bitcoin to the hackers in order to restore operations. Its significance is reflected in the fact that JBS provides one-fifth of all the beef and pork consumed in the United States. All these hacks are complicated by the fact that the US government has little contact with the private actors who are attacked, and the Russian government, among others, profits from and provides cover for hackers who agree not to attack it.
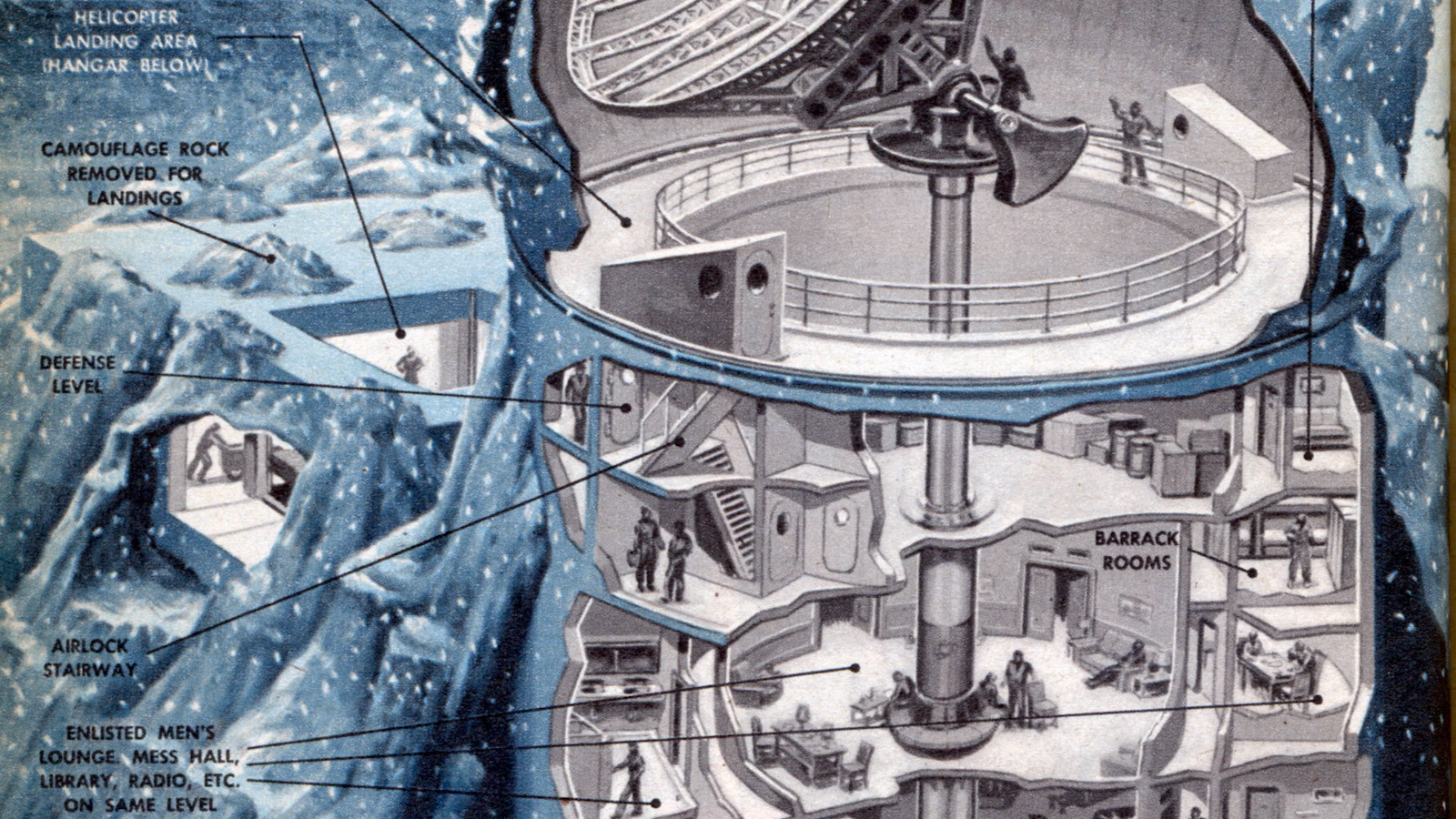
A fourth is state-sponsored sabotage of industrial firms, public utilities, and banks. The US-Israeli Stuxnet attack on Iran and the Russian attacks on Ukraine are leading examples. On June 17, 2010, Iranians began to report a machine stuck rebooting itself over and over again, designed to sabotage centrifuges (critical industrial control systems integral to the purification of radioactive uranium). This “Stuxnet” was the first case of cyber sabotage (the use of digital code developed to destroy something physical) and was believed to have then been part of a sustained US campaign of cyber operations against the Iranian nuclear program known as the Olympic Games, which began during George W. Bush’s presidency and continued through Barack Obama’s.
In the past few years, Ukraine has experienced a plethora of cyberattacks from Russia that have targeted and harmed Ukrainian media, finance, transportation, military, politics, electricity, and energy. These attacks have been calculated and conducted in an attempt to sabotage and control Ukraine.
A fifth is cyber political campaigns designed to influence or disrupt political processes or support separatist movements. These directly target “political independence” and “territorial integrity” and thus trigger powerful norms against aggression and in favor of self-defense responses. In 2016, in a famous instance of this, Russia was found to have influenced the 2016 US election via Facebook. The primary effects were that thirty-nine state voter databases, the Clinton campaign, the Democratic National Committee, and the Democratic Congressional Campaign Committee were hacked. Politically damaging information was released and spread as propaganda on social media outlets, and some regions’ polling stations halted because of tampering on the day of the election. The FBI became aware of these Russian overseas cyberattacks months prior to the election but was unable to halt and prevent the pervasive attacks coming from many different hackers.
In early 2018, twelve Russian intelligence officers were charged with hacking by the US Department of Justice, although the Kremlin denied any involvement. These attacks continued.